Cloud providers, specially those ranked higher like Microsoft Azure, Alibaba Cloud or Amazon Web Services, tend to follow very scrupulously all regulations everywhere they have a data center or PoP (point of presence).
In the case of Alibaba Cloud, we are talking about a big number of those, both international and regional certifications to assure their customers and users their data is in a good safe. Alibaba Cloud adheres to international information security standards and is committed to using international best practices as shown here. As an example, they were the first cloud computing company in the world to obtain C5 attestation in Germany. Not a small feat!

Knowing this, one should rest assured their data is going to be and stay safe on the cloud. We can say the cloud is home to very sensitive data, and trusting companies to hold them for us should come with an assurance that they will be responsible for protecting it. The McAfee “Cloud Adoption and Risk Report” of 2019 stated that there is a jump in all data-sensitive activities in the cloud like files shared or company threats.
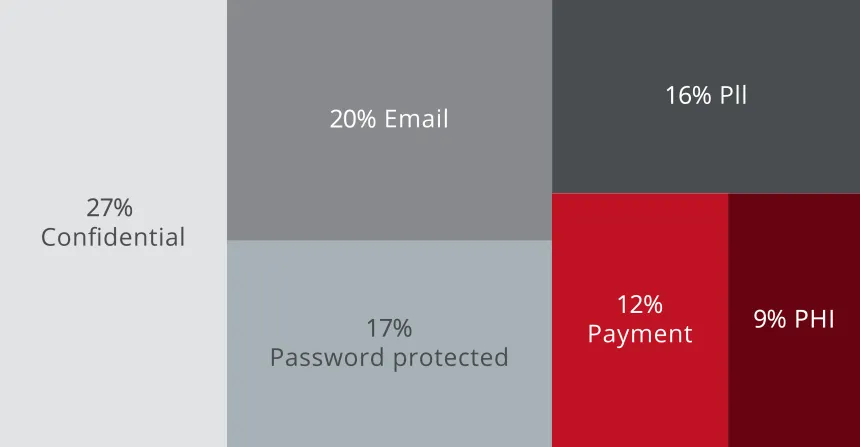
As for the types of sensitive data stored in the cloud, 27% are confidential, 20% emails, 17% password protected, 16% PII, 12% payment and 9% PHI. Everything very serious stuff.
What If You Need/Want More Protection
Fair enough. We live in a world where there are more and more data breaches and you shouldn’t rely 100% on others if you don’t really feel is acceptable for you. Other reasons are that, by company policy or contracts with clients, you are required to go one step further in terms of protecting your data.
For those and even more reasons… Please welcome Alibaba Cloud KMS (Key Management Service). According to Wikipedia, key management “refers to management of cryptographic keys in a cryptosystem. This includes dealing with the generation, exchange, storage, use, crypto-shredding (destruction) and replacement of keys. It includes cryptographic protocol design, key servers, user procedures, and other relevant protocols”.
Creating a key
This is the first obvious step to use the KMS functionality. Once in the KMS console, click “Create Key” and fill the details like “Key Spec”, “Alias Name”, “Protection Level”, “Rotation Period” and wether you are letting Alibaba generating the key or otherwise you will upload your own.
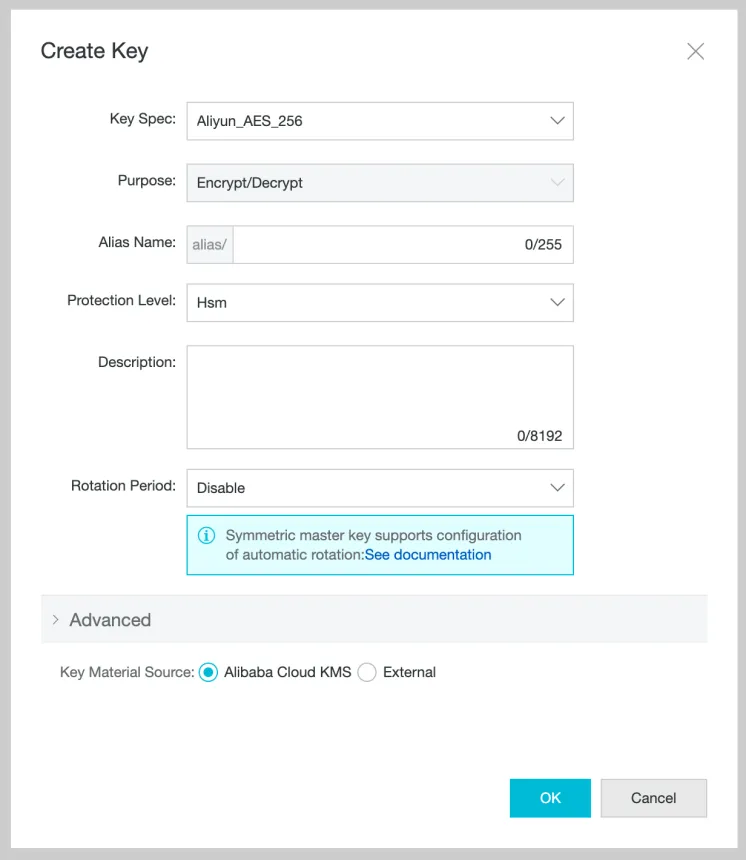
Options:
- Key Spec: Aliyun_AES_256, Aliyun_SM4, RSA_2048, EC_P256, EC_P256K & EC_SM2
- Alias Name: An alias can contain letters, numbers, and underscores (_), hyphens (-), and forward slashes (/).
- Protection Level: Software or HSM (Hardware).
- Rotation Period: Disabled or 7 to 730 days.
- Key Material Source: Alibaba Cloud KMS or External (You can import a 256-bit symmetric key).
BYOK (Bring Your Own Key)
This would be the highest level of security in terms of data ownership you could have, as the key wasn’t even generated in the cloud but your computer instead. If you choose “External” as “Key Material Source”, you will need to upload later the key from your computer. Remember that you can import a 256-bit symmetric key only when “Aliyun_AES_256” or “Aliyun_SM4” are chosen in the “Key Spec” parameter.
Conclusion
We learnt today that, if not strictly required, not using a key management service like the one Alibaba Cloud provides still gives you an outstanding level of security given the numerous audits and certifications they have in order to protect your data. KMS is useful when a contract depends on your using it, like a government-level usage or some extra compliance you want to achieve.
Enjoy the cloud and protect your data!